The Hidden IT Costs of Keeping Legacy Logistics Software in ‘Read-Only’ Mode
1. Why Obsolete TMS and Customs Systems Are Kept on Life Support
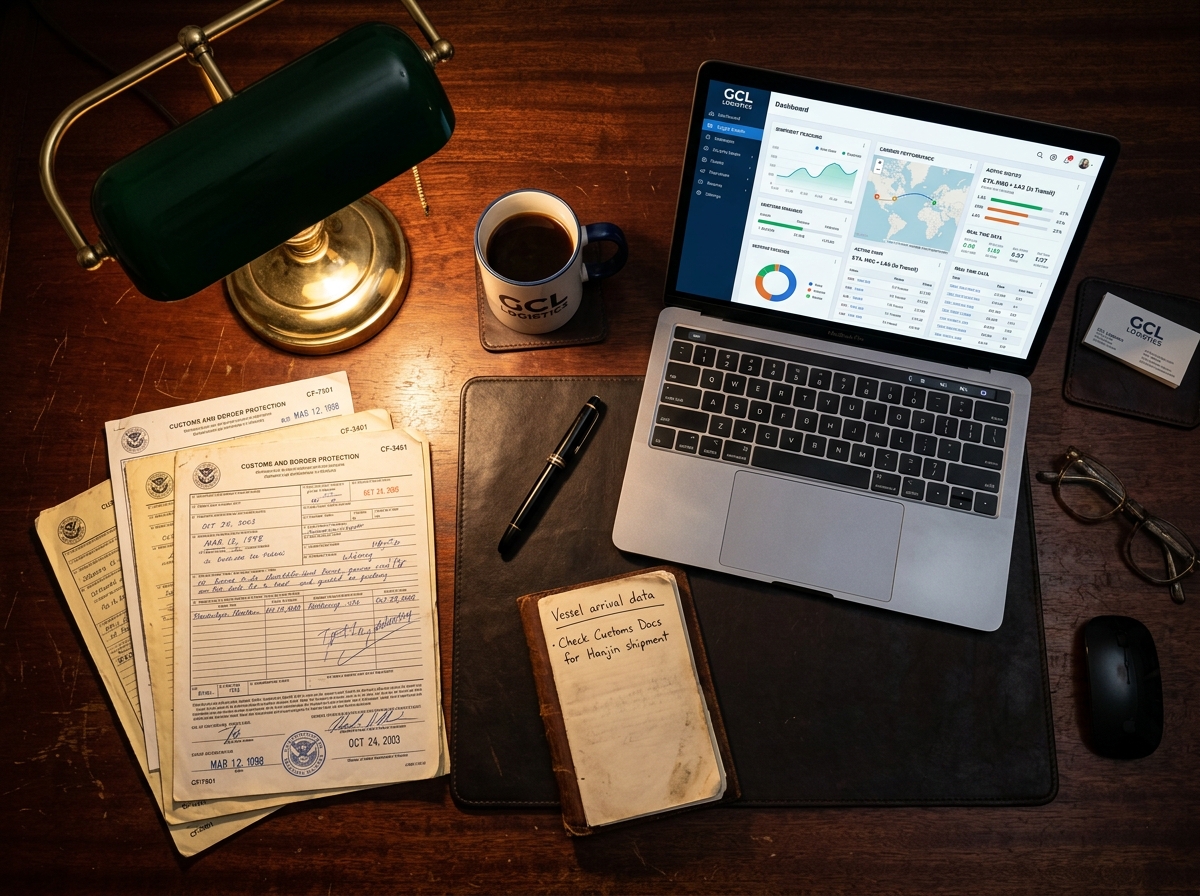
When logistics organizations migrate their active workflows to a new Enterprise Resource Planning (ERP) platform, historical files are frequently left behind on the old server. This technical debt is often the result of strict customs record-keeping regulations, which make cleaning up or migrating customer data a highly sensitive task. Fiscal documents and customs clearance records are legally required to be retained for seven years. To avoid complex data migrations, freight forwarders often take the path of least resistance: freezing their legacy Transport Management System (TMS) and switching it to a ‘read-only’ or ‘view-only’ license. This ensures fiscal data remains accessible for government audits, saving data engineers the effort of restructuring the legacy archive to fit the new data model.
However, this practice turns dormant back-office systems into silent budget drains. According to a 2024/2025 Pegasystems study, cited in the analysis Outdated Systems Cause Hundreds of Millions in Losses for Companies, organizations unnecessarily keep up to twenty deprecated applications running this way. Additionally, an advisory report by AcICT, detailed in AcICT Publishes Guidelines for Tackling Legacy Systems, emphasizes that ignoring this phase-out process leads to unmanageable IT environments. While active processes successfully move to the cloud, the empty shell of the legacy software remains locally hosted, monthly chipping away at server budgets, electricity, and network management capacity.
The Friction Between ERP Migrations and Statutory Retention Periods
Modern logistics platforms operate on database architectures that differ fundamentally from applications built a decade ago. Porting old NCTS or AGS customs declarations requires specific data transformations, forcing IT architects to remap and re-index countless fields. Whether automated or handled manually, migrating ten years of customs history demands extensive preparation—a reality that frequently conflicts with the strict go-live deadlines of a new TMS.
Faced with these constraints, project managers often decide to initiate only active files in the new platform during the transition phase. From that point on, the frozen legacy platform acts as a digital vault opened only a handful of times a year. Users no longer input new data, the system performs zero calculations, and it adds absolutely no value to daily supply chain operations. The statutory retention period justifies keeping the server around, but this technical “life support” strategy quietly drives up monthly overhead costs.
2. The Hard Truth About Legacy Maintenance Costs
A dormant system still requires the exact same foundational pillars as a live production environment: licenses, hosting, and IT man-hours. Once the vendor classifies the software as ‘end-of-life’, standard support contracts are voided. From that moment, vendors charge premium rates to provide incidental support or essential stability patches. Physical servers or compartmentalized cloud environments run continuously, burning through storage capacity and electricity. Internal network specialists dedicate hours every week updating firewalls, verifying backups, and managing authorizations for a system that is operationally dead.
A financial analysis inevitably shows that these hidden operating expenditures accumulate rapidly. Benchmark data from Score Agency, detailed in What Does Annual Software Maintenance Cost?, indicates that software maintenance typically consumes 15 to 20% of the initial development investment every year. Furthermore, insights from Escalating Management Costs for Legacy Systems: Where Does It End? confirm that unstructured maintenance causes these costs to spiral out of control the moment hardware needs replacing or compatibility issues with modern operating systems arise.
The Hidden Costs of Read-Only Software
- License Increments (End-of-Life Penalties): Vendors actively discourage the use of depreciated legacy versions by frequently increasing the pricing of read-only modules.
- Server Maintenance: Reserved capacity on physical infrastructure or older cloud servers drains monthly budgets via constant power consumption and storage allocation.
- Wasted IT Man-Hours: System administrators burn highly valuable time maintaining and securing platforms that offer no active business value—time that is subsequently lost for strategic new implementations.
Calculation Example: The TCO Over a Seven-Year Period
The financial impact becomes glaringly obvious when mapping out the Total Cost of Ownership (TCO) across the mandatory customs retention period. A freight forwarding firm is faced with a binary choice: leave a passive application running on their network, or initiate a dedicated data extraction project.
| Cost Component (Annual) | Scenario A: Read-Only Maintenance | Scenario B: Data Extraction & Archiving |
|---|---|---|
| Read-only & Support License | € 4,500 | € 0 |
| Server / Cloud Hosting | € 2,400 | € 300 (pure data storage) |
| IT Management Hours (patching & checks) | € 3,100 (approx. 40 hours) | € 0 |
| Total Annual Cost | € 10,000 | € 300 |
| Cumulative TCO (7 Years) | € 70,000 | One-off extraction (€ 8,000) + € 2,100 = € 10,100 |
The calculation above clearly illustrates the capital leak occurring throughout the mandatory retention period. While simply maintaining the system guarantees access to the legacy user interfaces, the massive seven-year price tag does not outweigh the benefits of a controlled, one-off project to store data in a centralized archive or data lake.
3. Risk Management: Security Breaches as Financial Liabilities
Beyond direct budget impacts, an outdated software layer poses a critical compliance risk to the continuity of your broader corporate network. When support from the original software developer ceases, the application no longer receives critical security updates. Ransomware gangs and automated network scanners actively hunt for easily exploitable ports left behind by unpatched software. An isolated, dormant TMS can easily act as a stepping stone into the freight forwarder’s active operational network.
A 2025 analysis by IT consultancy Vasco Consult, published as Old Systems: Silent Costs, Major Risks, specifically warns against the severe lack of governance surrounding these dormant network nodes. Unmanaged data archives can directly lead to major GDPR violations if personal data (such as the addresses of international recipients) is leaked or remains unprotected and accessible to unauthorized personnel.
Vulnerabilities Driven by a Lack of Patch Management
Running software without active vendor support essentially leaves an open door for external threats. Network protocols that were considered robust and secure five years ago now harbor Common Vulnerabilities and Exposures (CVEs) that hackers actively exploit. While IT administrators often apply stopgap measures—such as isolating systems via Virtual Local Area Networks (VLANs) or deploying additional firewalls—these extra security layers do not resolve the vulnerability of the underlying data. As a logical next step to maintain a healthy IT infrastructure, it is crucial to prioritize cleaning up or migrating customer data, enabling your organization to permanently pull the plug on legacy systems.


